FAQ
Frequently Asked Questions
1. What is InfoSec?
Information Security or InfoSec is protecting the IAC Integrity, Availability and Confidentiality
2. Is it IT Security?
IT Security or Information Technology Security is only in the IT infrastructure whereas Information Security focuses on the entire organisation.
IT Security is only a small part of the organisational or information security.
3. What is AppSec?
Application Security is enabling the secure coding principles to ensure the apps are secure before it gets released to the public.
4. What is Vulnerability Assessment?
Vulnerabilities or lack of counter-measures in the intact organisational security with the intent to alleviate them.
5. What is Penetration Testing?
Ensuring the overall layers of security of the organisation is protected by simulating like that of a malicious hacker without any intent to cause havoc. PT or Pen Test is imperative to ensure the business is secure and analyse the vulnerabilities and threats much earlier the real attack.
6. What is Information Security Management Systems(ISMS)?
Information Security Management Systems (ISMS). However, organisations foresee to go beyond IAC to shield fame or trustworthiness, preserve customers’ data, and ensure the steady operations by adhering to the enterprise continuity.
7. How will my organisation get benefitted by ISMS or ISO/IEC 27001:2013?
- It helps build a credibility with your customers.
- It helps for the business continuity and systems for disaster recovery.
- It helps you to build an excellent system that works like a charm.
8. Is ISO 27001 applicable for start-ups?
ISO/IEC 27001:2013 is a framework which you can build upon the system you want for any organisations.
9. What is a Back-door?
Backdoor is a sort of cyber-threat in that the attacker uses a back-door to install a keylogging software, thereby allowing an unlawful access to the system. This threat can turn out to be probably dangerous as it permits for alteration of the files, stealing information, introducing rejected software or even exercising control of the entire network.
10. What is a Denial-of-Service Attack?
A denial-of-service or a DOS attack usually means attacking the network to bring it down entirely with hopeless traffic by affecting the host device which is connected to the internet. A DOS attack targets websites or services which are hosted on the servers of banks and credit card payment gateways.
Information Security or InfoSec or CyberSecurity is very vast.
11. What is DDoS?
DDoS implies a Distributed Denial of Service. It is an endeavour to make any online service transitorily unavailable by forming overwhelming network traffic from multiple origins or discontinue services of a host connected to the internet.
12. What is a direct-access attack?
Whenever any criminal gets unauthorised access to the data centre and executes malicious software on the server, it is called the direct-access attack.
13. What is eavesdropping?
It is secretly overhearing a conversation in the system-of-networks that are secure.
14. What is Spoofing?
Spoofing is a cyber-attack where a person or a program imitate another by creating false data to gain illegal access to a system. Such threats are commonly found in IP where the IP address is spoofed.
15. What is Tampering?
Tampering is a web-based outbreak where explicit parameters in the URL are replaced without the customer’s awareness. Moreover, when the customer keys in that URL, it looks and appears the same. It is produced by hackers to rob the identity and capture unauthorised access.
16. What is a Repudiation-attack?
A repudiation attack transpires when the user denies the fact that they performed an appropriate action. A user can just refuse consciousness of the communication.
17. What is Information-disclosure?
Information-disclosure-breach implies that the information which is thought to be secured is discharged to corrupt elements that are not trustworthy.
18. What is a privilege-elevation-attack?
A privilege-escalation-attack is a type of network invasion that permits the user to have the root access to the system which was principally not permitted. The attacker understands the benefit of the programming errors and commands the admin privileges to the network.
19. What is an exploit?
An exploit could be a software sketched to take advantage of a vulnerability in the system. The critic plans to augment smooth access to a cyber system and gain control, allows privilege escalation or creates a DDOS attack.
20. What is Social Engineering?
The art of deception either by persuading or influencing people. The hacker gets the information of all the credentials. However, the victim will not be aware of it.
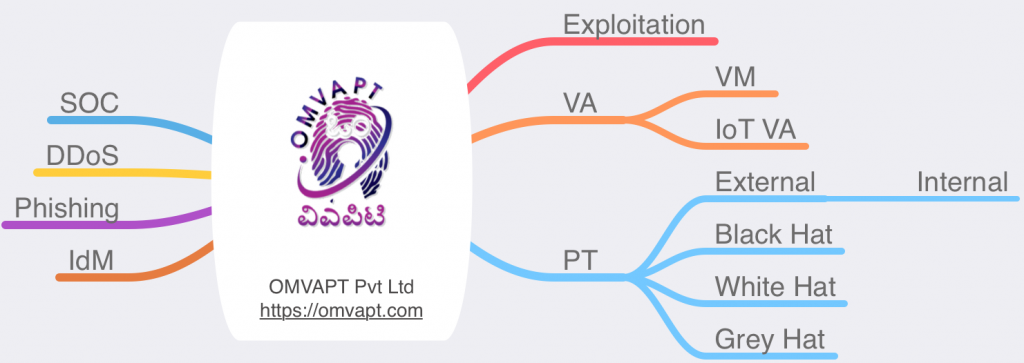
OFFENSIVE SECURITY OFFSEC IS FULLY OFFENSIVE IN NATURE. SUCH AS MALWARE ANALYSIS, REVERSE ENGINEERING, VULNERABILITY ASSESSMENT (VA), PENETRATION TESTING (PT) & DIGITAL FORENSICS
21. What is an Indirect-attack?
It is an attack launched from a third party computer as it becomes harder to track the origin of the attack.
22. What is a computer crime?
The offence is initiated with the use of a computer, and a network is called as a cyber crime.
23. What is a Malware?
Malware attributes to malicious software that is being designed to damage or perform unwanted actions on the system. It is of many types like viruses, worms, Trojan horses so on & so forth that cause havoc on a computer’s hard drive. They can either delete some files or a directory or simply gather data without the actual knowledge of the user.
24. What is an Adware?
Adware is a software that sponsors advertisements that render ads to its creator. It has commercials embedded in the application. So when the program is running, it shows the ad. Adware is similar to malware as it uses ads to inflict computers with deadly viruses.
25. What are Bots?
It is a software application that commands automated jobs that are simplistic and repetitious in nature. It may or may not be malicious, despite the fact that they are usually exposed to initiate a DDoS attack or a click fraud while using the internet.
26. What is a Ransomware?
Ransomware is a class of cyber security threat which will restrain admittance to the computer system in the beginning and will ask for a ransom for the restriction to be removed. This ransom is to be paid through online payment methods only which the user can be granted access to their system.
27. What is a rootkit?
It is malicious software designed in such a way that hides individual processes or programs from normal anti-virus scan detection and continues to enjoy privileged access to your system. It is that software that runs and gets initiated every time you boot your system and are difficult to detect and can install several files and processes in the system.
28. What is spyware?
Spyware is a software which typically spies and gathers information from the system through a user’s Internet connection without the user’s knowledge. A spyware software could be majorly a hidden component of a freeware program which can be downloaded from the web.
29. What is a scareware?
Scareware is a type of threat that operates as an absolute system message and guides you to download and purchase the useless and potentially dangerous software. Such scareware pop-ups seem to be similar to any system messages but aren’t. The primary purpose of the scareware is to create anxiety among the users and use that tension to coax them to download irrelevant software.
30. What is a Trojan Horse?
Trojan Horses are a sort of threat that are malicious or harmful programming codes hidden behind legitimate programs or data which can allow complete access to the system and can cause damage to the system or data corruption or loss/theft of data. It acts as a backdoor, and hence it is not readily detectable.
Other InfoSec arenas – Malware Analysis, Reverse Engineering, Digital Forensics, Designing Information Security Architecture, Cryptography.
31. What is a Virus?
VIRUS – Vital Information Resources Under Seize. A system virus is a self-replicating program that, if executed, replicates or even modifies by inserting copies of itself into the different computer file and infects the affected areas once the virus succeeds in reproducing. It can be dangerous as it spreads. It can infect the preponderance of the system in no time.
32. What is a computer worm?
The worm is a self-replicating program which relies on the network of equipment and performs malicious actions and spreads itself onto other computer systems. Worms primarily rely on security failures to access the infected system.
33. What is a Phishing?
Phishing is a cyber-threat which makes an attempt to gain sensitive information like passwords, usernames and other details for malicious reasons. It is an email fraud where the perpetrator sends a legitimate looking email and attempts to gain personal information.
34. What is Identity Theft?
Identity theft is a violation wherein your personal details are stolen, and these features are used to commit a fraud. An identity fraud is committed when a criminal imitates individuals and use the information for some financial gain.
35. What is Intellectual Property Theft?
Intellectual Property robbery is a theft of copyrighted material where it violates the copyrights and the patents. It is a cyber-crime to get hands on some trade secrets and patented documents and research. It is a theft of an idea, plan and the methodology being used.
36. What is a Password Attack?
It is a kind of a threat to your system or network security where enemies customarily try ways to augment access to your system credential hashes. They either simply presume the password or use a computerised program to find the correct password and gain entry into the system.
37. What is a Blue-snarfing?
Blue-snarfing is an explosion of information through illegal medians. The hackers can gain access to the information and data on a Bluetooth-enabled phone utilising the wireless technology of the Bluetooth without warning the user of the phone.
38. What is a Blue-Jacking?
Blue-jacking is just sending of texts, images or sounds, to another Bluetooth, enabled device and is an inoffensive style of marketing. However, there is a thin line among bluejacking and bluesnarfing, and if crossed, results in the act of threat.
39. What is a Keylogger?
A keylogger is a spy-ware that has the capability to spy on the events on the computer system. It can record every stroke on the keyboard, websites visited and every data accessible on the system. These recorded logs are then sent to a specified receiver.
- OMVAPT PRIVATE LIMITED is registered at Bengaluru, Karnataka, India.
- OMVAPT Pvt. Ltd. is an Information Security & Offensive Security company.
40. What is Man-in-the-middle-attack (MiTM)?
Through imitating the endpoints in an online information transfer (i.e. the connection from your smartphone to a website), the MITM can gather information from the end user and the object he or she is interacting.
41. What is Malvertising?
A method to jeopardise the computer with malicious code that is downloaded to the system when someone clicks on an affected ad.
42. What is a Watering-Hole attack?
It is a network attack strategy, in which a victim is a particular combination (organisation, enterprise, or region). In this attack, the attacker guesses or perceives which websites the group often uses and infects one or more of them with malware. Ultimately, some member of the targeted group gets infected.
43. What is a semantic attack?
It is the application of inaccurate information to undermine the credibility of target devices or to cause direct or indirect infliction. It is also the modification and promulgation of information to set someone into the illegal direction or to cover trails.
44. What is SPIM?
Spam Over Instant Messaging such as getting offensive messages on your Instant Messengers such as Skype, Messenger, Fb Messenger, Whatsapp, Google Hangouts so on & so forth.
45. What is SIEM?
Security Information & Event Management – Collection of logs from all servers, networking devices including, SAN (Storage Area Networks) & Network Attached Storage (NAS) as well as Unified Storage.
46. What is UBA?
User Behaviour Analytics – is the tracking, collecting and analysing of user data and activities by utilising monitoring systems. It gives security teams with actionable insights.